Forensics Explained
“What do you mean by ‘forensic’ - is it like CSI?”
Plain English
Forensic simply means using science to get to the truth. It's not all Bunsen burners and test tubes though, the forensic part of what we do applies more to the procedures and the scientific processes that we follow. These processes have been formalised in the ACPO Good Practice Guide for Computer-Based Electronic Evidence. If you work with computer evidence a lot, then you should be reasonably familiar with this. The guidelines boil down to three important principles:
1. Don't change anything
During our investigation, we will need to examine the device and probably take a copy of the data for analysis. Nothing that we do should make changes to the device or its data.
2. Some changes are inevitable
With some devices; mobile telephones and sat navs for example, changes to data cannot be avoided. Simply switching them on to capture the data will alter some dates and times. This is acceptable as long as the examiner is suitably qualified, knows what data will change and can explain the implications of those changes.
3. Ensure that work is repeatable
A cornerstone of any forensic process is to take thorough notes to ensure that the examiner can recall in detail what steps were undertaken, and so that another analyst can repeat the work and achieve the same results.
There is a fourth principle which states that the person running the investigation is responsible for ensuring the first three are followed. But in reality, it falls to the analyst to do this. these guidelines are certainly something you should ask any prospective forensic analyst about before commencing work for you. If they seem a little vague about them, then find someone else!
How does it all work then?
When a computer, mobile telephone, satellite navigation system, laptop, digital camera, sever or any device capable of storing data is used to retrieve, edit or store that data, then those actions leave traces of activity. Even deleting data leaves traces of the command used to carry out the deletion. In forensics, this is known as Locard's Principle; the idea that “every touch leaves a trace”.
Our forensic scientists use the latest tools and techniques, some of which we have developed, to analyse these traces and provide a compelling narrative of exactly what happened on a device during the period in question.
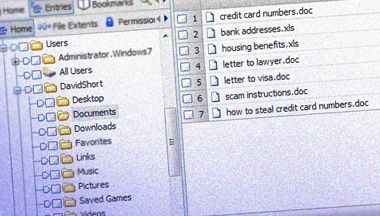
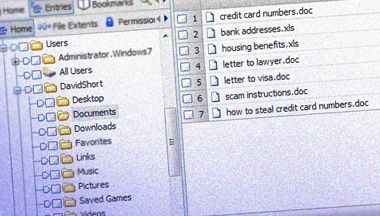
We have a lot of experience in analysing the data embedded in files that most people aren't aware even exist. For example, the editing details stored in Office documents, the GPS location data embedded in digital photographs, the timestamps encoded within Internet history, the unique user identifiers associated with computer files, and so on.
It's certainly the case that forensics is an arms race between software developers creating new ways to manage data and forensic analysts reverse engineering data structures to accurately understand how the data that is present came to be.
Our processes are all about discovering the truth, so in cases where the accounts of those involved are less than reliable, we are very well placed to assist you sort truth from fiction, based on scientific fact.
When do I need a forensic investigation?
The most important decision you need to make is whether or not you need a forensic analyst, or digital investigator to examine the computer equipment in question. If you believe that a computer or other data storage device has been used by one or more of the people involved in the situation you're looking at, then the chances are that a forensic examination will help.
Take a Human Resources case we looked at recently as an example:
An employee at an investment bank claimed that another employee was sending harassing messages to them. These messages were sexual in nature and highly distressing. A brief examination by the IT email team showed that no email had been sent or received on the corporate email systems. Those involved were adamant that the massages “must be on the computer somewhere”. We were asked by the HR Manager to look into this further, where we discovered that Facebook Chat had been used. Given the nature of the allegation, discretion was important, so we forensically copied the hard disks (a process known as imaging) of both the machines at night after the employees had gone home.
Our analysis of the Facebook chat artefacts present showed that the allegation was completely without merit. We recovered chat messages to friends of the complainant saying she was thinking of leaving and had figured out a way of getting a nice payout from the company before she left. We found further messages to the other staff member, essentially goading him into a sexual conversation which she then used as the basis of her complaint. Taken out of context, the message extracts seemed quite damning, but when seen as a whole, the overall intent was very clear.
When presented with our findings, the employee admitted the scam and resigned. This saved the company a potential loss of reputation and a financial payout. It saved the victim the distress of trying to prove his innocence and ensured that any follow up action by the complainant could be dealt with in a straightforward manner as an independent investigator had been instructed, negating any claims of constructive dismissal.
We have a collection of other casework for you to read for more insight into the process.
What to do next?
Call us now on 020-8166-0059 or send us an email and we'll call you straight back to discuss how we can help.
Even if you don't need our services now, have a look at our forensic readiness section to make sure you have everything in place to best respond to an incident in the future.